Evasi0n jailbreak is undoubtedly the most popular untethered jailbreak of all time.
Supporting a range of iOS devices, Evasi0n gave us the freedom we wanted to modify our iPhone, iPad, or iPod Touch with free and easy access to heaps of Cydia tweaks and apps – it took time to get to us, but it was well worth the wait.
Supported Devices:
Evasi0n jailbreak works on these devices:
- iPhone 3GS, 4, 4S, 5
- iPad 2, 3, 4, and Mini
- iPod Touch 4G, 5G
Content Summary
Download Evasi0n App:
Evasi0n jailbreak is easy to download, and we’ll give you the complete steps in just a minute. First, you can download Evasion jailbreak from the link below:
- Evasi0n Mac (ver. 1.0.8) link above.
- Evasion Windows (unavailable). Please try Posixspwn
How to Install Evasi0n Jailbreak:
Before jailbreak your device, ensure that you have updated iTunes to the latest version and back your data up using iTunes, iCloud, or both.
Follow the steps below to install Evasion jailbreak on your iPhone, iPad, or iPod Touch:
- Download Evasi0n jailbreak onto your computer using the link above and save it to the desktop.
- Double-click on the zip file and extract Evasi0n to your desktop folder
- Click the Evasion app to open it ( for Windows, right-click and choose Run as Administrator )
- Disable your device passcode for the duration of the jailbreak, and then connect the device to your computer
- Check that Evasi0n has detected your device and confirmed the iOS firmware on it
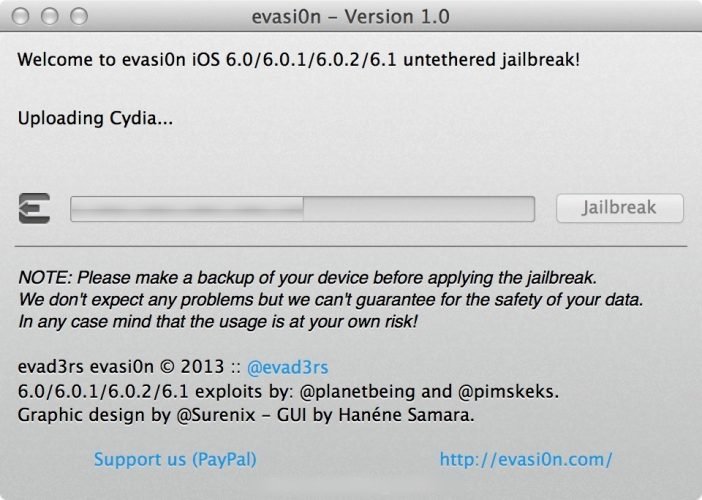
- Click on the big Jailbreak button
- Leave your device – you can see a progress bar on the screen. The jailbreak may take a few minutes, so don’t do anything on your computer either.
- When you see the message asking you to unlock your device, do so but DO NOT close the Evasion tool down.
- Tap the Evasi0n icon on your device home screen; you will see a black screen for a second or so, and then the application will exit – do not worry, this is just part of the process.
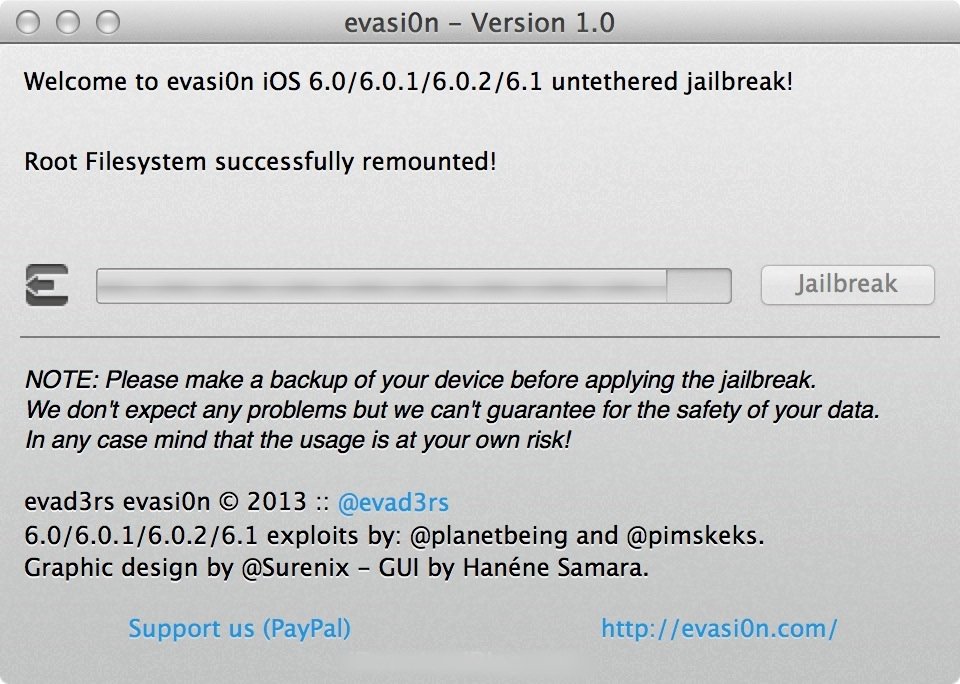
- Again, you will see a progress update of the jailbreak on your screen as it happens.
- You will see a message that tells you the jailbreak is complete; expect a few restarts on your device throughout.
- When your device has rebooted, an Evasion logo will appear, showing you jailbreak status messages.
- Your device will reboot once more, and several more status messages will appear on the screen.
- When your device has rebooted for the last time, you will see the Cydia icon on your home screen, and you can start using it.
Please be patient; the entire process can take a while and must not be interrupted. If it does stop working (the screen has frozen, or it is stuck on one part for several minutes), you can do a hard reset on your device and start again.
Evasi0n Jailbreak Errors:
Evasi0n jailbreak is pretty smooth, but users have reported one or two errors. Here, you will find details of those errors and solutions:
- Patching Kernel Issue
If your jailbreak process appears to be frozen on “Patching Kernel,” be patient; some users have reported that part of the process takes around 18 minutes to complete. If it takes a lot longer, hard reset your device by pressing the power and home buttons together until it reboots.
- Finding Offsets
This is also a part of the jailbreak that may take a while to complete, up to 10 minutes in some cases. As above, if it takes a much longer time, hard reset the device and start again.
- Cydia Errors
Some users have reported problems with not being able to log into their Cydia account or the “My Accounts” page not being visible. This is down to the jailbreak team repository owners to solve so you will need to be patient. In some cases, setting your DNS to the 8.8.8.8 Google servers may solve the problem.
- Jailbreak Button is Greyed Out
Some users report seeing this even when they have connected their device. Before you start, go into iTunes and disable the password protection on your iTunes backups – you can enable it again after the jailbreak.
- Weather App
This affects the iPad – a second Weather app may show up after the installation. This is nothing to worry about; the app is there as it should be and maybe hidden inside a configuration file. Other users have reported that their Weather app crashes after installing Evasi0n. Check Cydia for updates in the first instance and apply any that are available. Other than that, we will need to wait for a fix, and that will be made available on this page as and when we have it.
- Endless Reboot Loop
This is an irritating issue to some users, and there are a couple of ways to fix it. Find full details about how to fix an endless reboot loop.
The main issue with the reboot loop lies within MobileSubstrate. Up to now, MobileSubstrate has not been tested thoroughly with Evasi0n jailbreak, and if any of the Cydia apps have not been updated to support the new firmware, they will not work. There are a couple of things you can do to fix this:
- Avoid using Evasi0n jailbreak until the issue has been fixed
- If you do install Evasi0n, don’t use any apps that have not been updated with the relevant firmware support.
This should fix the above problem and let you use the jailbreak easily.
- Device Stuck at Apple Logo
This is a common issue with the Evasi0n jailbreak and is easy to solve. First:
- Do not use the OTA method when you update your firmware as it is not compatible with Evasi0n jailbreak. Always update using iTunes instead.
- Always back your device up and restore it using iTunes before you attempt the jailbreak.
How to Fix:
- Using the correct cable, connect your iPhone, iPad or iPod Touch to your PC or Mac
- On your iOS device, press and hold the Home and Power buttons together for about 10 seconds
- Release the power button but hold the Home button until the Device in Recovery message appears in iTunes
- Hold the SHIFT or ALT button on your keyboard and click Restore on the iTunes window
- Wait for your device to be restored and then try Evasi0n jailbreak again.
If it still doesn’t work, you will need to wait for an update to Evasi0n jailbreak
General Troubleshooting Tips:
- Make sure that you disable to passcode on your device before you install Evasi0n as it can interfere with the process
- While the jailbreak is going ahead, do not run XCode, iTunes, iPhone Configuration Utility or TinyUmbrella
- If the jailbreak gets stuck, you can safely do a hard reset of your device and start the process again
This page will be kept updated as needed, and you can get the latest updates by liking the page on Facebook, clicking Following > See First so that published updates will show on your newsfeed.